Do you know why several serverless and platform-as-a-Service (PaaS) services are favored today? The answer is because they eliminate several operational burdens and create budget efficiency. Though this sounds simple enough, when it comes to security, things can get a little complex.
Companies make use of PaaS to streamline the development of application services, RESTful APIs, and all components that provide business logic. While some definitions involve traditional web hosting or a few elements of it in the PaaS bucket, from a security-oriented point of view, securing your PaaS use is closely tied to securing the underlying application supported by PaaS.
To start with, your PaaS security checklist must include contractual negotiations with your provider and review and validation of the vendor environments and processes. This will also enable the vendor to identify your existing security models and security-relevant tools available to you.
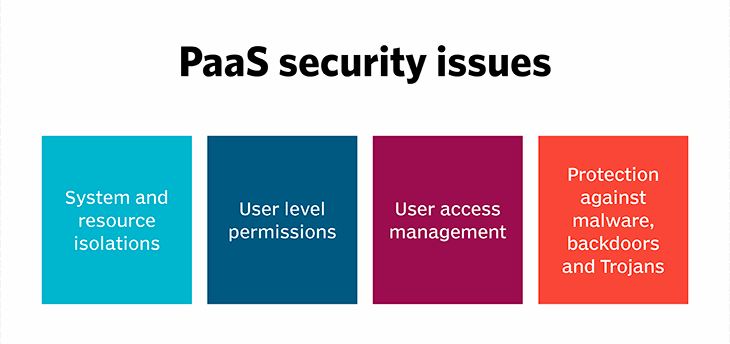
You must know that all cloud use cases require similar security precautions, and these are not unique to protecting PaaS. However, on top of these, IT security teams must focus equally on the application itself. This makes PaaS much more challenging to secure than any other cloud model.
PaaS security strategies can vary from accommodating the business environment to business context to industry usage. However, here are a few PaaS security best practices that can be applied in almost every situation. Implementing these five steps can help to ensure that your applications are built and run safely in a cost-efficient way.
Threat Modeling
Your application security or PaaS must start with threat modeling. This systematic approach deconstructs your application design into multiple component parts and analyzes how these parts communicate through a cyber attacker’s eye. In assessing the application’s components and associated risks, threat modelers can map mitigation steps to remediate unknown vulnerabilities.
Irrespective of which PaaS providers you are dealing with or for what purpose, building a well-organized threat model adds value. If required, your InfoSec team can update application security testing approaches to extend threat modeling to microservices and mesh architecture.
Data Encryption at rest and in transit
Most providers offering PaaS services either enable or require the client to encrypt data in transit. REST APIs, which interact making use of HTTPS as the transport, are the gold standard architectural style in application development, particularly in a cloud computing scenario. In contrast, “stored data” is less ubiquitously approached. Wherever possible, encrypt your stored data, irrespective of your customer data or configuration or session information. In PaaS, encrypting data at rest requires your security teams to embrace tools specific to the PaaS providers’ APIs.
Finally, after encrypting the data at rest and in transit, you must pay sufficient attention to secrets management. This refers to the keys generated and used to implement at-rest encryption, as well as API tokens, passwords, and other artifacts that must be kept secure.
Mapping and testing interactions across the business flow
Making use of multiple cloud service providers is no longer a rarity but the norm today. For instance, an enterprise can employ serverless at the edge for its A/B testing, AWS Lambda to execute business logic, Heroku to serve the UI, and more for different tasks. Therefore, creating and consistently updating a complete diagram of interactions is crucial. This process can support PaaS security best practice as threat modeling involves creating a data flow diagram to depict how components communicate.
To ensure all elements are adequately covered during penetration testing, your InfoSec team must systematically test every component holistically and in isolation.
Portability to Avoid Vendor Lock-in
PaaS faces an unusual challenge because its supported features (security services, underlying APIs, and language choice) depend on the particular PaaS in use. For instance, one PaaS provider supports Java and Python, while another supports C#, Go, and JavaScript.
PaaS consumers rarely can “drop in and replace” because of the underlying platform APIs. Therefore, it is necessary to use a language that is commonly supported across all providers. This helps in maximizing portability and minimizing vendor lock-in. Like Python, C#, and Java, frequently used languages are supported by all providers. Hence, it would be best to create wrappers around niche APIs to execute a layer of abstraction between an application or service and the underlying niche APIs. This indicates that, while changing providers, only one change needs to be made instead of making hundreds or thousands of changes.
Advantage of Platform-specific Security Features
PaaS offerings are also different from each other in terms of the security features they provide. A user must understand what options are available and, wherever possible, it is imperative to enable them. Few PaaS platforms offer a web application firewall or application gateway that can be turned on to protect applications and services better. At the same time, others can offer improved logging and monitoring capacities. Here’s why InfoSec leaders must identify which security options are offered and then take advantage of them.
Final Thoughts
A PaaS model requires an identity-centric security process that varies from enterprises’ strategies in traditional on premise data centers. Effective measures such as developing security into the applications, providing adequate internal and external protection, and monitoring and auditing the activities must be included in PaaS security approaches to win your war against the security risks. Evaluating the logs helps you to identify security vulnerabilities as well as improve opportunities. Ideally speaking, your InfoSec team must address any threat or vulnerability beforehand so that no attackers can see and exploit them.